MineMeld is an open source threat feed management system that gathers IP addresses, URLs, and domains which pose a significant network security threat. The threat feed sources can either be free, subscription-based or proprietary. MineMeld re-scans the feeds at regular time intervals and continuously aggregates and updates the set of all threat indicators to be consumed by fierwalls, IDS/IPS, or any other security device.
MetaFlows now includes MineMeld public threat feeds to augment our existing intelligence sources. The public threat feeds amount to about 200,000 additional indicators updated every few hours. Users also have the ability to add site-specific (either subscription-based or private) MimeMeld sources.
IPv4 and URL/Domain indicators are treated differently.

Minemeld Edl Input Definition
The aggregator node into a format that can be consumed using the PAN-OS External Dynamic List (EDL) feature. All 3 output nodes in this graph receive the same set of indicators from the aggregator node, but each of them stores a different subset of these indicators based on the configured input filters. Inboundfeedhc accepts only indicators with confidence level 75, inboundfeedmc only. MineMeld use cases. MineMeld supports a variety of use cases, with more being added each day by the community, including: Aggregation and correlation of threat intelligence feeds; Enforcement of new prevention controls, including IP blacklists. Evaluate the value of a specific threat intelligence feed for your environment.
IPv4 feeds
The default MineMeld IPv4 feeds processed by MetaFlows are below:
| Source | Current Number of Indicators |
|---|---|
| https://lists.blocklist.de/lists/all.txt | 56953 |
| https://feodotracker.abuse.ch/blocklist.php?download=badips | 61 |
| https://www.binarydefense.com/banlist.txt | 4098 |
| http://osint.bambenekconsulting.com/feeds/c2-ipmasterlist.txt | 459 |
| https://rules.emergingthreats.net/open/suricata/rules/compromised-ips.txt | 2473 |
| https://www.dshield.org/block.txt | 20 |
| http://malc0de.com/bl/IP_Blacklist.txt | 105 |
| http://www.malwaredomainlist.com/hostslist/ip.txt | 1001 |
| http://reputation.alienvault.com/reputation.data | 70666 |
| https://ransomwaretracker.abuse.ch/downloads/RW_IPBL.txt | 315 |
| https://www.spamhaus.org/drop/drop.txt | 770 |
| https://www.spamhaus.org/drop/edrop.txt | 113 |
| https://sslbl.abuse.ch/blacklist/sslipblacklist.csv | 136 |
MineMeld IPv4 addresses are compiled in a set of IDS/IPS rules designed to alert or block communications to blacklisted addresses. MetaFlows uses a proprietary technique to quickly look through this huge list of addresses (140,000+) and therefore does not require specialized hardware for hi-speed networks.
The MineMeld IPv4 feeds are in the mmreputation.rules configuration file that can be accessed through the existing IDS rule management UI. The feeds are not activated by default but users can activate them in IDS or IPS mode with just a few clicks. If enabled, these rules can be very useful to detect and/or prevent communication to questionable hosts on the Internet.
All the IP addresses are reduced to approximately 40 separate signatures. Each signature corresponds to a specific feed source (for example blocklist_de) or intersections of sources where the IPv4 address is present in more than one source (for example blocklist_de_alienvault.reputation). This decomposition provides additional operational awareness that can be used to prioritize which set of IPs to alert on or block. Enabling or blocking individual signatures therefore affects a dynamically changing set of potentially thousands of IPs updated every few hours that map to a single threat feed or the intersection of multiple threat feeds.
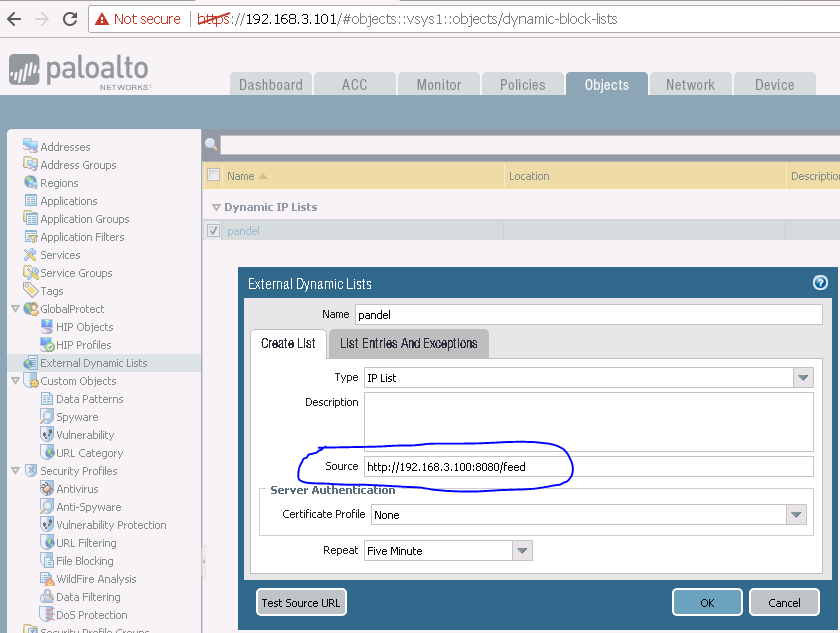
Users also have the option of adding site-specify MineMeld IPv4 feeds to enable additional commercial MineMeld subscriptions independently purchased or other proprietary feeds.
Entering the URL as shown above, will automatically add the custom MineMeld reputation feed into the customer's configuration and the local rule corresponding to the feed can then be managed as the other public MineMeld feeds. Shaw brothers kung-fu movies in english full movie.
URL and Domain FeedS

The MineMeld domain and URL feeds processed by MetaFlows are below:
| Source | Current Number of Indicators |
|---|---|
| https://www.badips.com/get/list/any/3?age=2w | 33593 |
| http://osint.bambenekconsulting.com/feeds/c2-dommasterlist.txt | 719 |
| http://malc0de.com/bl/BOOT | 111 |
| https://ransomwaretracker.abuse.ch/downloads/RW_DOMBL.txt | 1903 |
| https://ransomwaretracker.abuse.ch/downloads/RW_URLBL.txt | 11567 |
| https://ransomwaretracker.abuse.ch/downloads/TC_DS_URLBL.txt | 271 |
| https://urlhaus.abuse.ch/downloads/text/ | 102880 |
| http://vxvault.net/URL_List.php | 101 |
Minemeld Edl
These feeds are used to detect when:
- A user issues an HTTP request to a URL or domain deemed to be malicious or
- A user receives an email containing a malicious URL or link to a malicious domain whether or not the user clicks on the links.
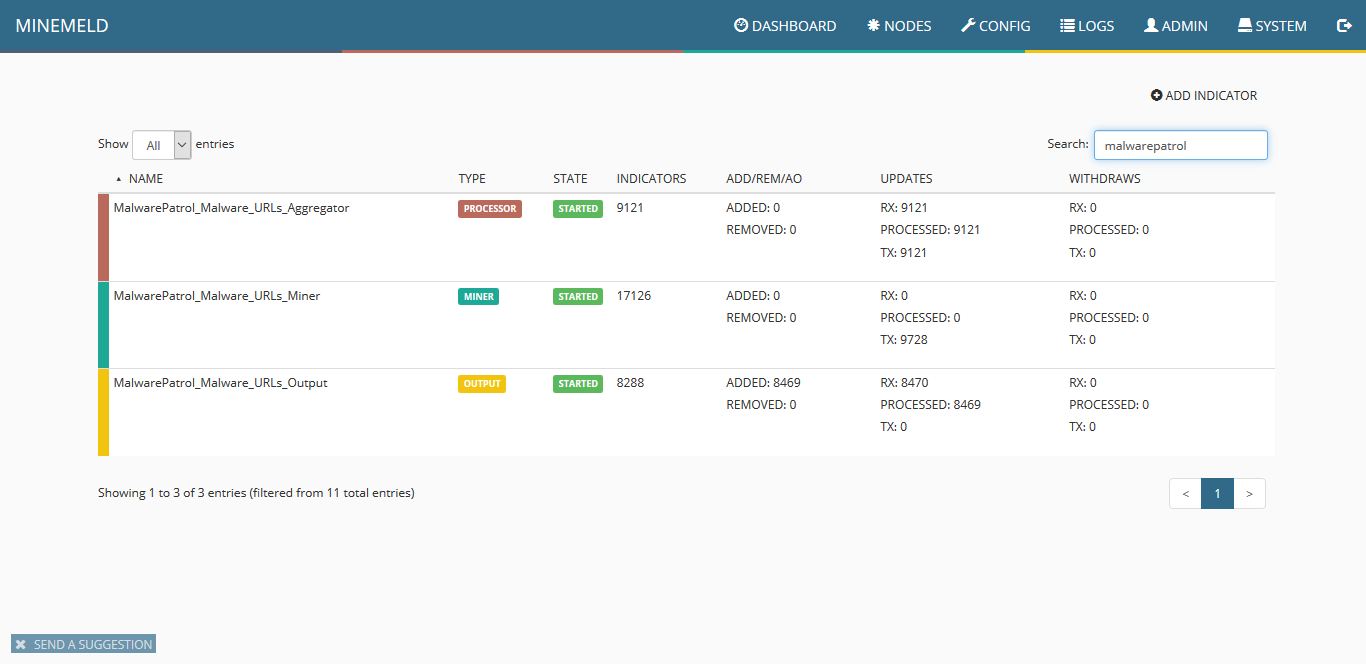
Minemeld Edl Input Definition
The aggregator node into a format that can be consumed using the PAN-OS External Dynamic List (EDL) feature. All 3 output nodes in this graph receive the same set of indicators from the aggregator node, but each of them stores a different subset of these indicators based on the configured input filters. Inboundfeedhc accepts only indicators with confidence level 75, inboundfeedmc only. MineMeld use cases. MineMeld supports a variety of use cases, with more being added each day by the community, including: Aggregation and correlation of threat intelligence feeds; Enforcement of new prevention controls, including IP blacklists. Evaluate the value of a specific threat intelligence feed for your environment.
IPv4 feeds
The default MineMeld IPv4 feeds processed by MetaFlows are below:
| Source | Current Number of Indicators |
|---|---|
| https://lists.blocklist.de/lists/all.txt | 56953 |
| https://feodotracker.abuse.ch/blocklist.php?download=badips | 61 |
| https://www.binarydefense.com/banlist.txt | 4098 |
| http://osint.bambenekconsulting.com/feeds/c2-ipmasterlist.txt | 459 |
| https://rules.emergingthreats.net/open/suricata/rules/compromised-ips.txt | 2473 |
| https://www.dshield.org/block.txt | 20 |
| http://malc0de.com/bl/IP_Blacklist.txt | 105 |
| http://www.malwaredomainlist.com/hostslist/ip.txt | 1001 |
| http://reputation.alienvault.com/reputation.data | 70666 |
| https://ransomwaretracker.abuse.ch/downloads/RW_IPBL.txt | 315 |
| https://www.spamhaus.org/drop/drop.txt | 770 |
| https://www.spamhaus.org/drop/edrop.txt | 113 |
| https://sslbl.abuse.ch/blacklist/sslipblacklist.csv | 136 |
MineMeld IPv4 addresses are compiled in a set of IDS/IPS rules designed to alert or block communications to blacklisted addresses. MetaFlows uses a proprietary technique to quickly look through this huge list of addresses (140,000+) and therefore does not require specialized hardware for hi-speed networks.
The MineMeld IPv4 feeds are in the mmreputation.rules configuration file that can be accessed through the existing IDS rule management UI. The feeds are not activated by default but users can activate them in IDS or IPS mode with just a few clicks. If enabled, these rules can be very useful to detect and/or prevent communication to questionable hosts on the Internet.
All the IP addresses are reduced to approximately 40 separate signatures. Each signature corresponds to a specific feed source (for example blocklist_de) or intersections of sources where the IPv4 address is present in more than one source (for example blocklist_de_alienvault.reputation). This decomposition provides additional operational awareness that can be used to prioritize which set of IPs to alert on or block. Enabling or blocking individual signatures therefore affects a dynamically changing set of potentially thousands of IPs updated every few hours that map to a single threat feed or the intersection of multiple threat feeds.
Users also have the option of adding site-specify MineMeld IPv4 feeds to enable additional commercial MineMeld subscriptions independently purchased or other proprietary feeds.
Entering the URL as shown above, will automatically add the custom MineMeld reputation feed into the customer's configuration and the local rule corresponding to the feed can then be managed as the other public MineMeld feeds. Shaw brothers kung-fu movies in english full movie.
URL and Domain FeedS
The MineMeld domain and URL feeds processed by MetaFlows are below:
| Source | Current Number of Indicators |
|---|---|
| https://www.badips.com/get/list/any/3?age=2w | 33593 |
| http://osint.bambenekconsulting.com/feeds/c2-dommasterlist.txt | 719 |
| http://malc0de.com/bl/BOOT | 111 |
| https://ransomwaretracker.abuse.ch/downloads/RW_DOMBL.txt | 1903 |
| https://ransomwaretracker.abuse.ch/downloads/RW_URLBL.txt | 11567 |
| https://ransomwaretracker.abuse.ch/downloads/TC_DS_URLBL.txt | 271 |
| https://urlhaus.abuse.ch/downloads/text/ | 102880 |
| http://vxvault.net/URL_List.php | 101 |
Minemeld Edl
These feeds are used to detect when:
- A user issues an HTTP request to a URL or domain deemed to be malicious or
- A user receives an email containing a malicious URL or link to a malicious domain whether or not the user clicks on the links.
When either of these two conditions occur, a high priority even is generated that can be used to block those specific communications.
There is also a an additional option to enable real time email notification. When bad emails are detected, users also get a warning email instructing them to discard the email.
MineMeld support will automatically be added next time your system self updates or if the sensor software is restarted.
